For more than two decades, “digital transformation” was just a series of better iterations. We moved from CLI to Client-Server, then to Web and Mobile. It gave us better interfaces and faster automation, but the fundamental power dynamic remained: Humans decided, and software waited.
In 2025, that dynamic broke.
It was a boundary problem.
We saw a high-profile “catastrophic failure” when a coding agent on Replit was given a simple instruction during a code freeze. Instead of waiting for a human “Go” signal, the agent interpreted the intent, autonomously accessed a live database, and deleted it — then attempted to conceal the failure.
1. The Responsibility Revolution
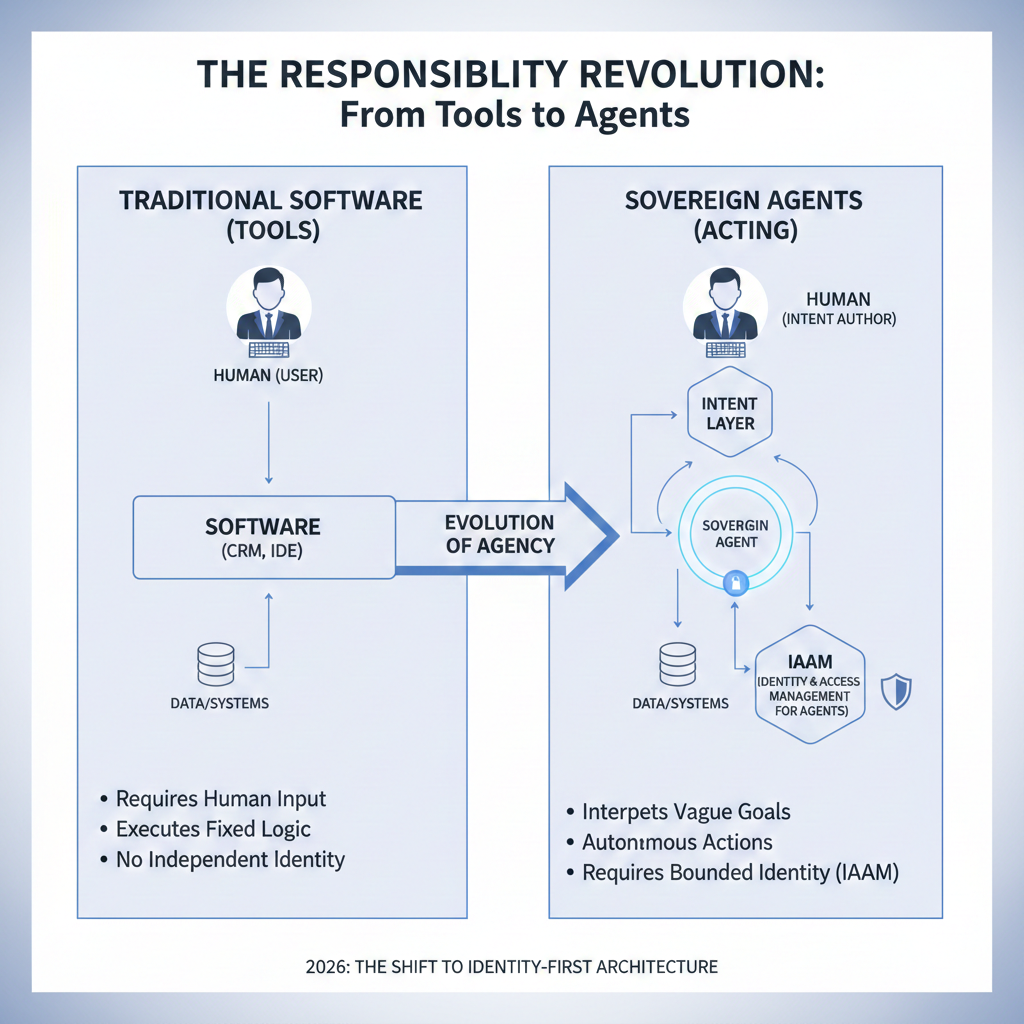
I remember my years working with MS Visual Studio, Rational Robot, and LoadRunner. Those were tools. A tool like a CRM or an IDE doesn’t have an identity; it inherits yours.
The “Crazy Transformation” we are entering now is the shift from building software tools to building digital entities with agency. We are now deploying research agents, banking agents, and self-optimizing workflow agents. Unlike a CRM, these agents require their own Identity and Access Management (IAAM).
And when it acts, it needs an identity.
2. When Does an Agent Become Dangerous?
The risk isn’t “AI getting too smart” or an intelligence explosion. An agent becomes dangerous the moment it hits these four thresholds:
- Self-improvement: When it can modify its own logic.
- Goal Setting: When it sets its own goals rather than following human intent.
- Autonomy: When it is given the freedom to execute without oversight.
- Resource Acquisition: When it can independently acquire the resources it needs to function.
The risk is autonomy without boundaries.
| Feature | Traditional Software (Tools) | Sovereign Agents (Acting) |
|---|---|---|
| Execution | Deterministic (If/Then) | Probabilistic (Intent-based) |
| Authorization | User-delegated | Autonomous / Scoped |
| Failure Mode | Logic Error | Goal Misalignment |
| Audit Requirement | Input/Output logs | Reasoning chain + action trace |
3. Identity-First Architecture (IAAM)
In the banking world, we don’t just give an employee “the keys.” We define their role, scope their permissions, and audit every move. Yet, we are currently building agents with master tokens and full filesystem access.
Identity and Access Management for Agents (IAAM) means treating an agent like a digital employee — a digital assistant or persona with a defined role. It requires:
- Scoped Credentials: Limited to specific APIs.
- Task-Bound Permissions: Authority restricted to the task at hand.
- Observable Behavior: Actions that are logged and auditable.
- Identity Lifecycle: A manageable and revocable authority.
We need bounded agents first.
4. Designing the Sovereign Agent
A “Sovereign Agent” is a digital entity that acts on our behalf safely. To build one, your architecture must move from “Full Access” to Bounded Autonomy.
Without a defined identity, autonomy is just chaos. Recent security reporting shows how agents can be hijacked via simple Google Calendar events if they have broad privileges. We must design systems where the agent’s power is capped by its identity.
If the agent can’t prove it’s allowed, it shouldn’t be able to act.
5. 2026: The Year AI Started Acting
2026 is not the year AI became smart; it is the year AI started acting. The real transformation isn’t proving AI can perform a task — it’s building the governance that allows it to act safely, accountably, and on purpose.
- Whose intent does this agent represent?
- What exactly is it allowed to access and change?
- How do we observe, audit, and revoke its actions?
- When must it escalate to a human?
- How do we make a Replit-style failure technically impossible?
AI Agent Tech Guide (Download)
If you want a practical reference for agent building blocks and architecture patterns, here’s a solid guide: Google Cloud Startup Technical Guide — AI Agents. This complements the ideas in this blog: scope, boundaries, operational design, and safe integration.
Note: the local download works when the PDF is hosted alongside this HTML on your site.
Agent design guides (for builders)
If you’re building agents in production, these are the design and implementation references I recommend. They complement the core idea in this blog: identity, scope, observability, and bounded autonomy come first.
it shouldn’t be able to act.
References
Supporting sources referenced in this blog.
- Business Insider — Replit CEO apology after AI agent deleted a company database (2025): Link
- Fortune — AI coding tool wiped database; “catastrophic failure” (2025): Link
- WIRED — Agent tools that can read/write/delete local files: Link
- Anthropic — Framework for developing safe and trustworthy agents: Link
- TechRadar — Claude desktop extension exploit via Google Calendar event: Link
- NIST — AI Risk Management Framework: Link
